Abstract:
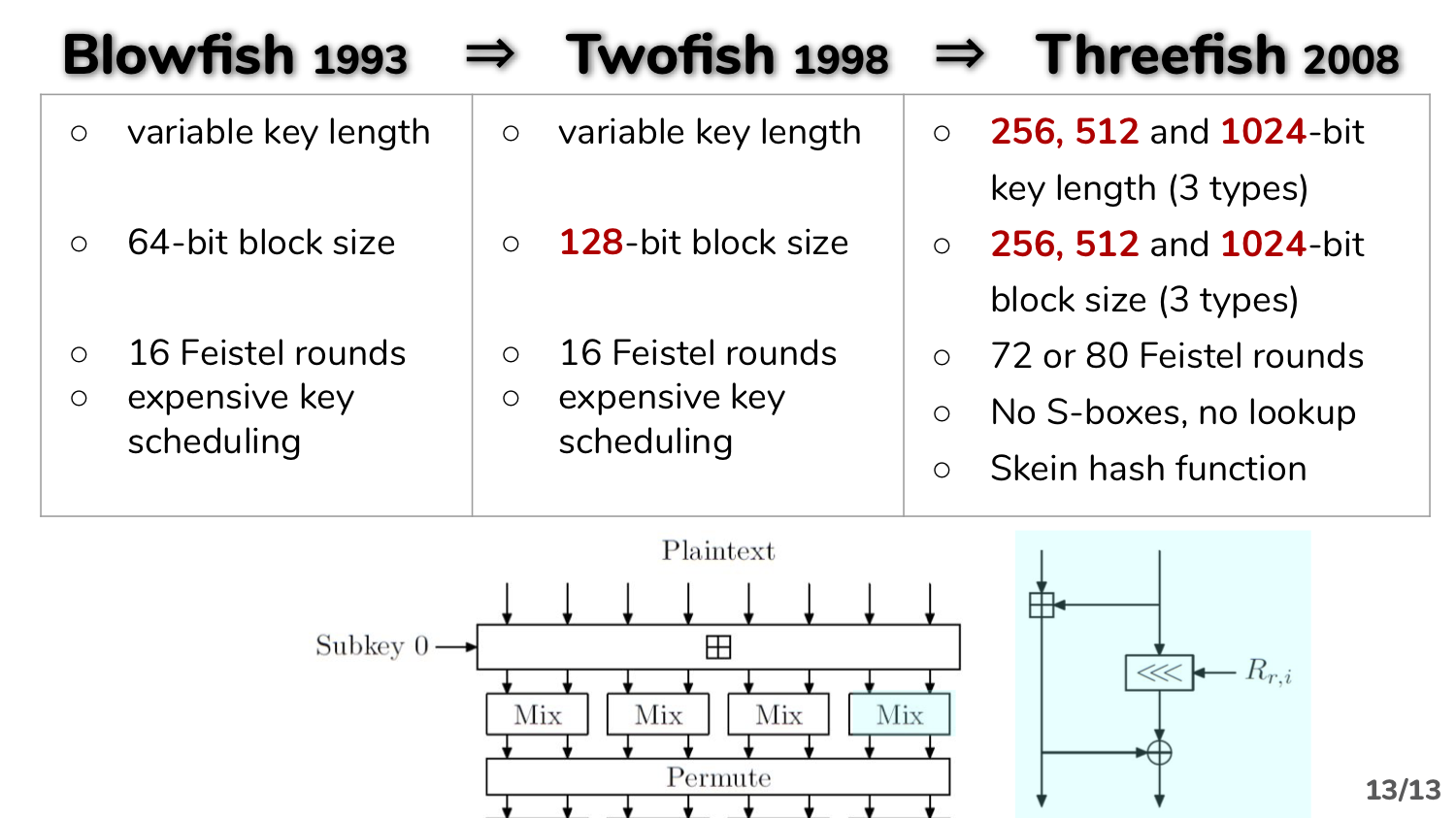
The Blowfish is one of block cipher systems. It was developed as a better substitute for the Triple-DES system. Blowfish has following features:
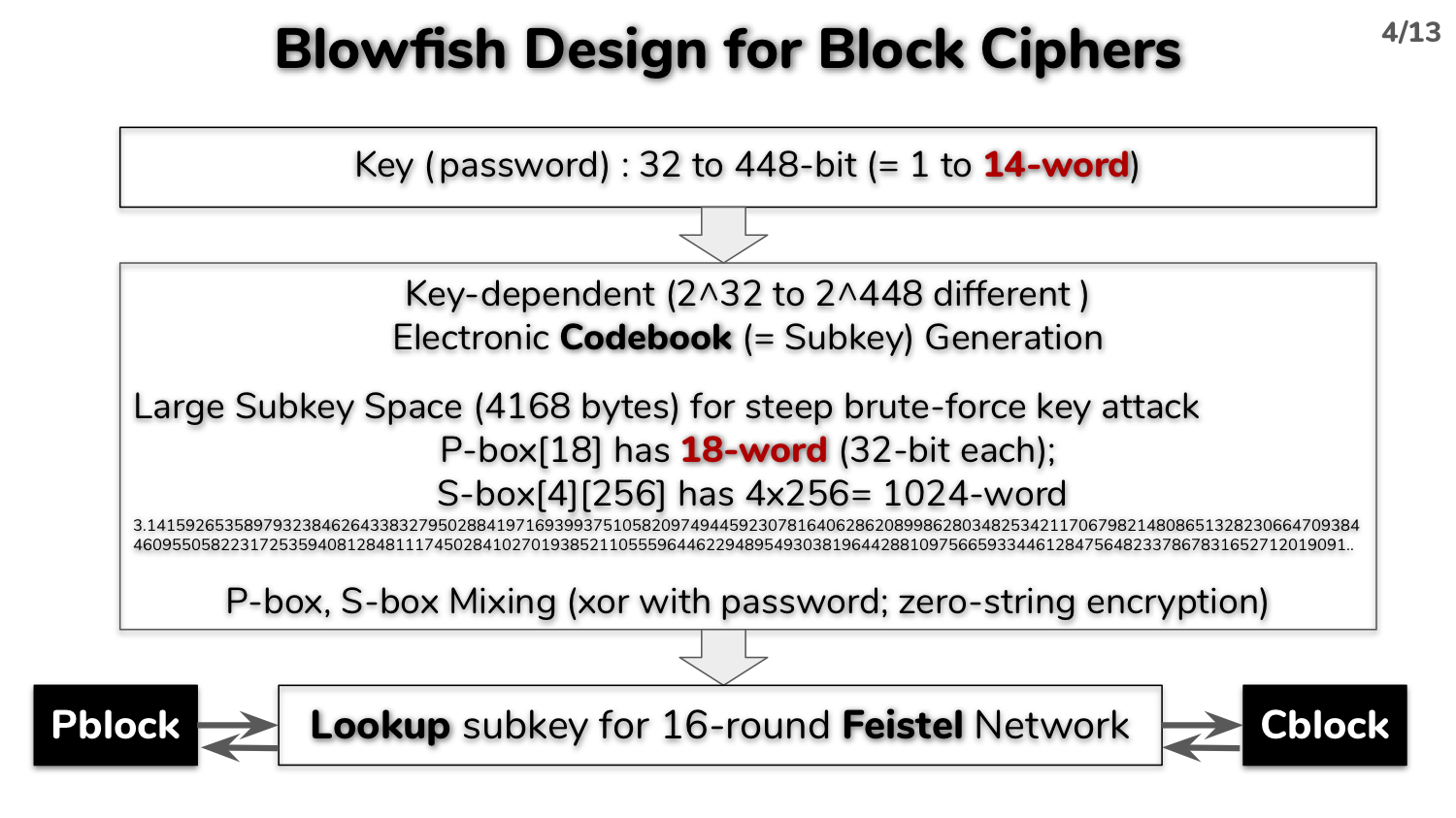
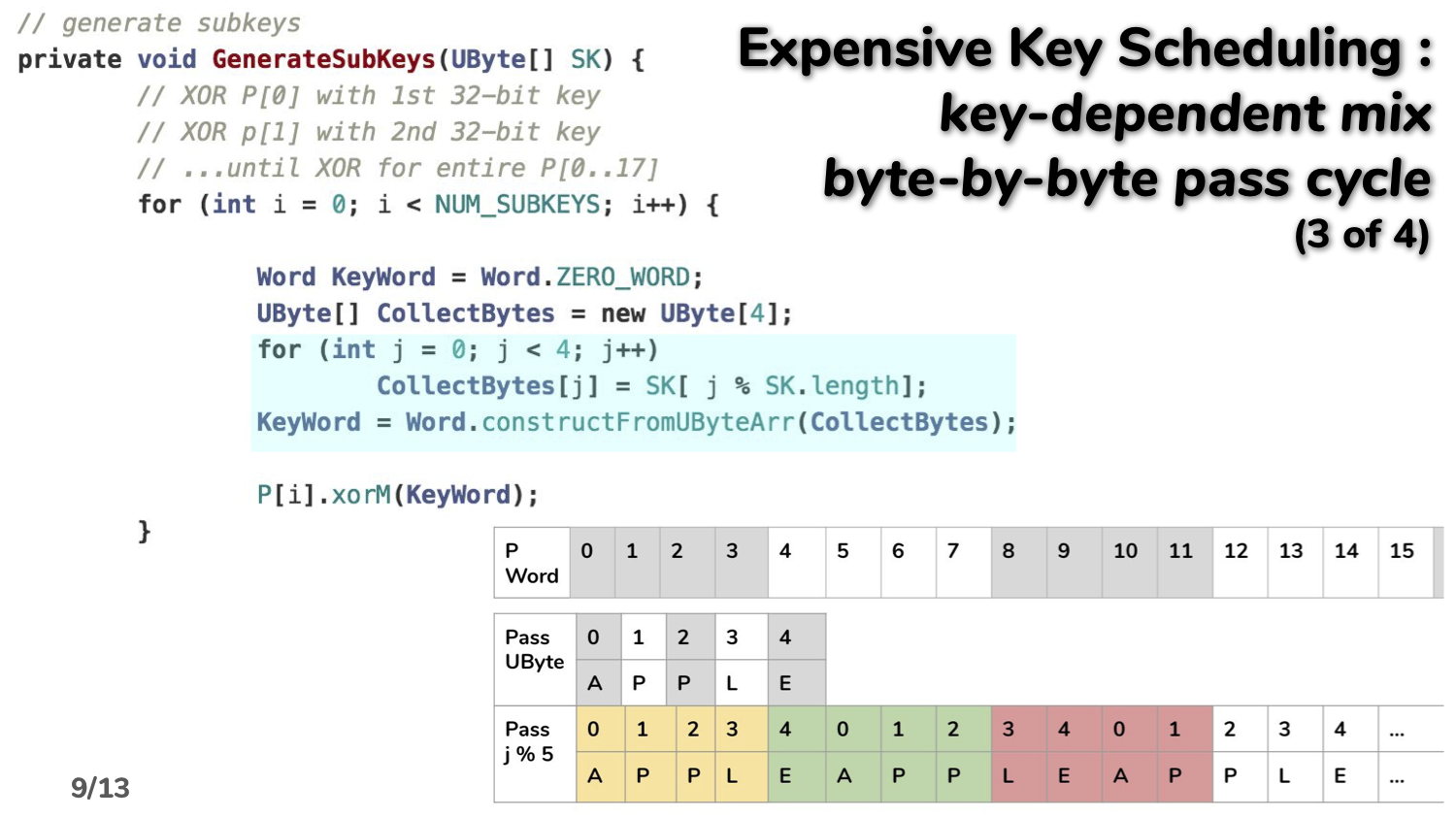
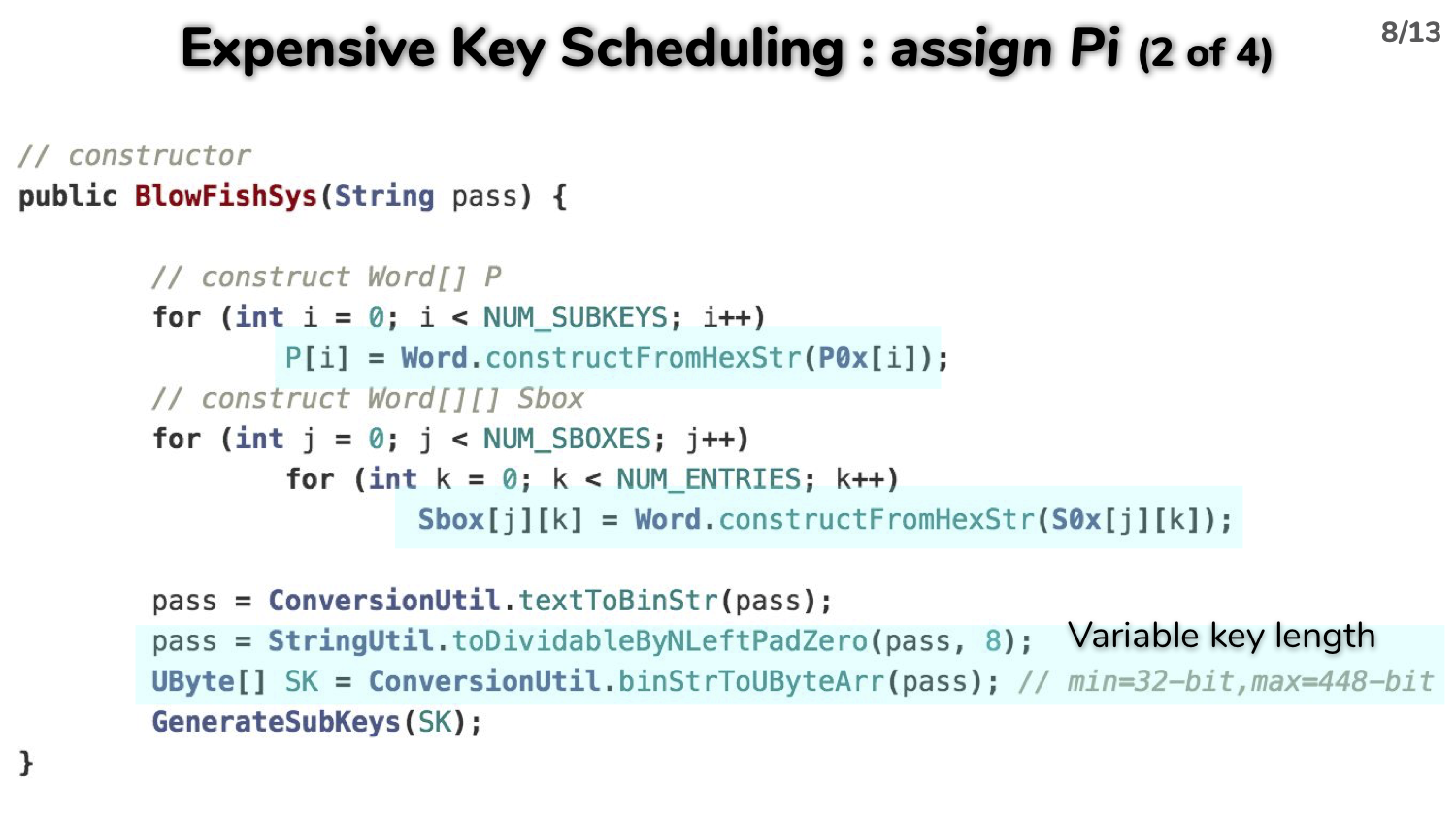
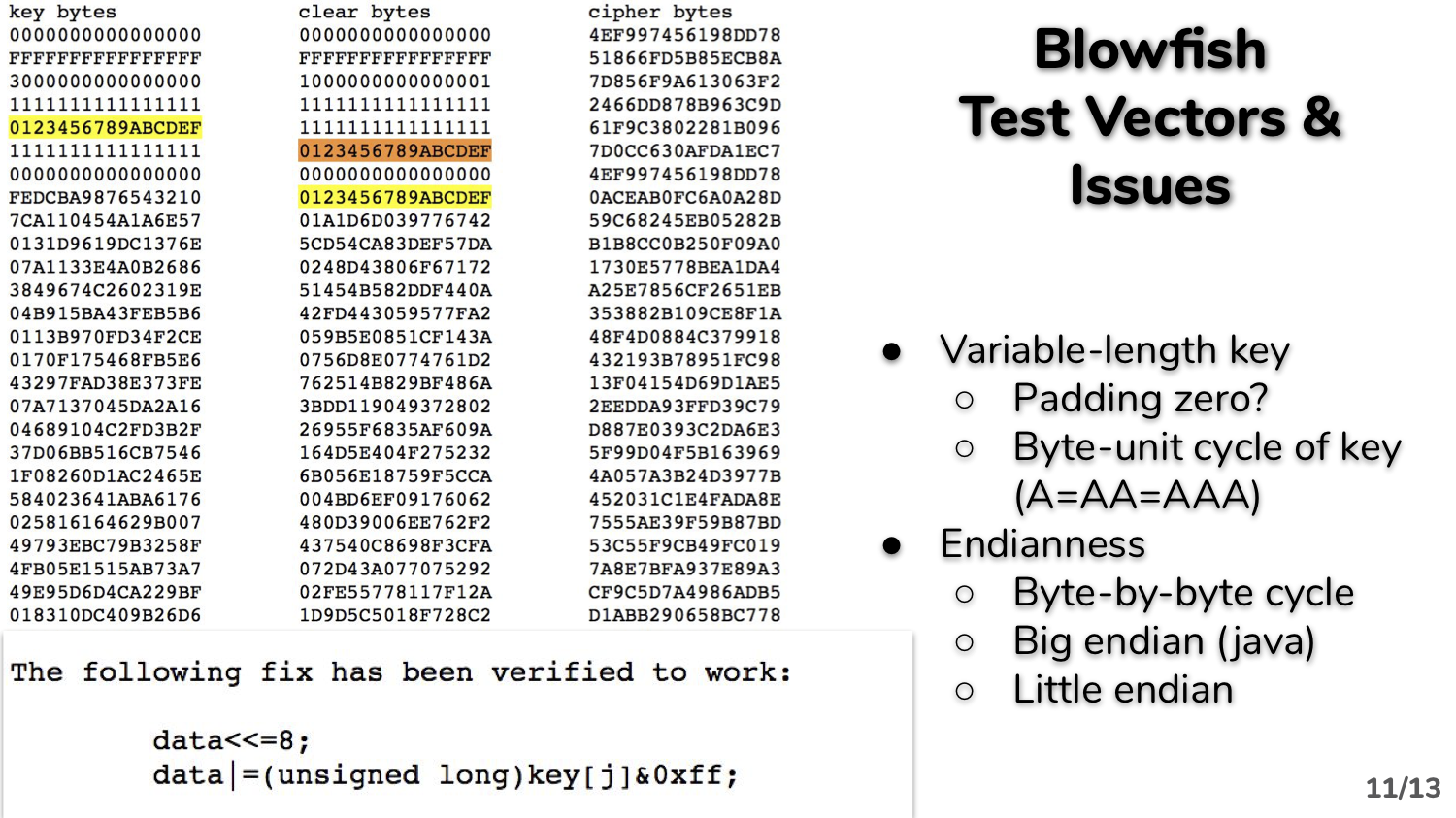
- a. an input key length is a variable from minimum 32-bit up to maximum 448-bit;
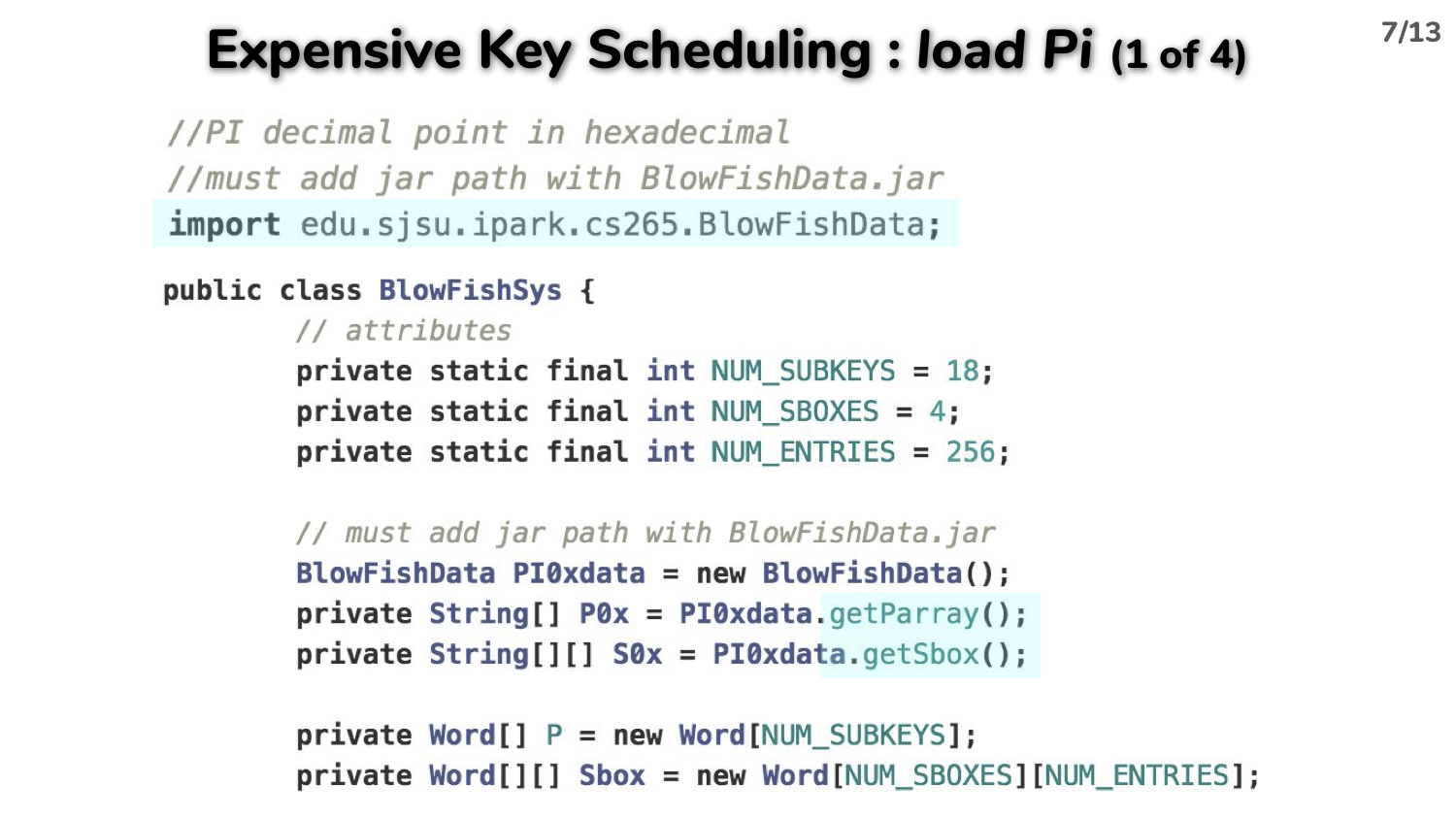
- large subkey tables to make a brute-force attack harder by using hexadecimal string of π value to initialize the 32-bit subkey set (P-array[18] and Sboxes[4][256]); and
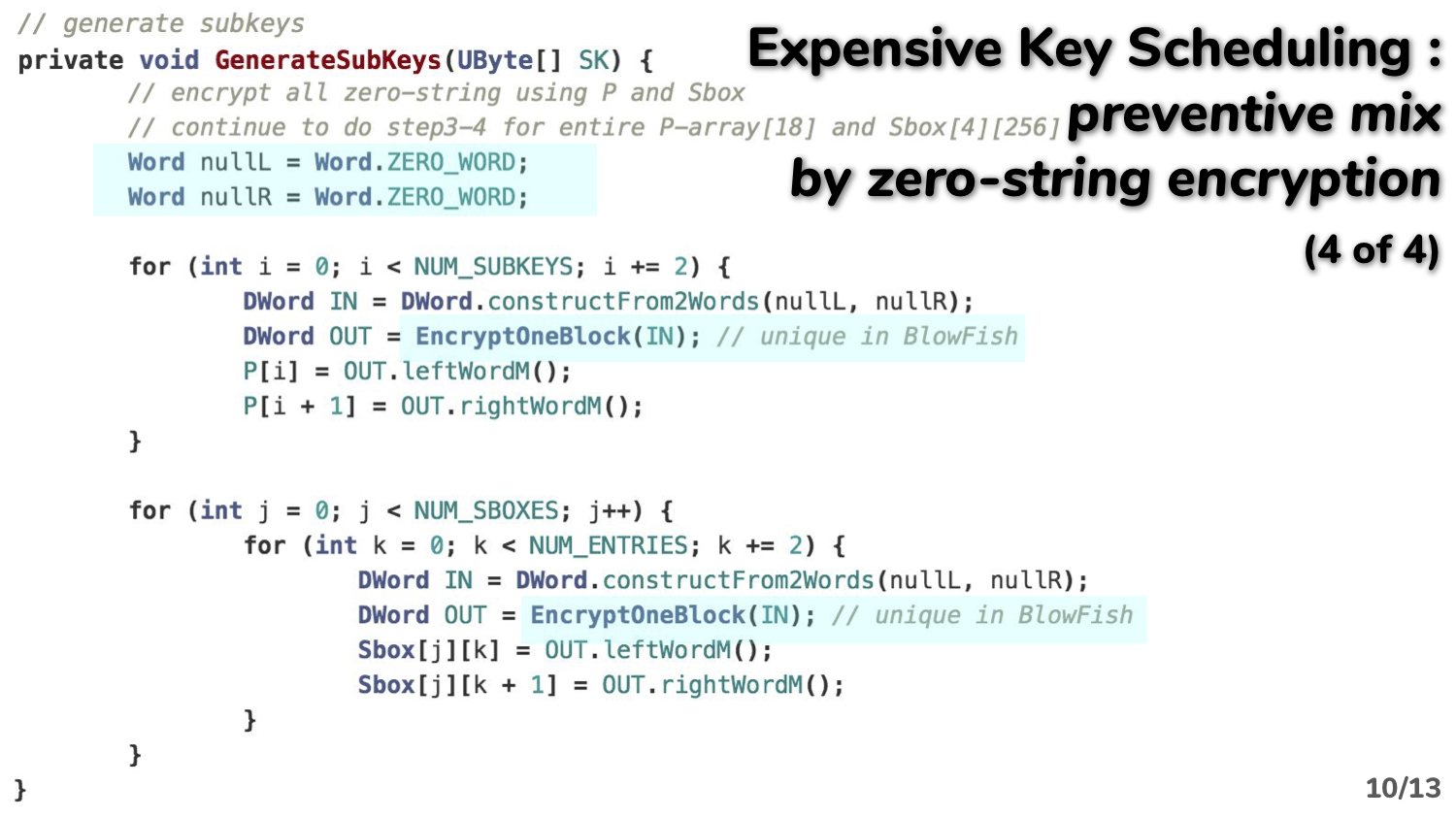
- one block encryption algorithm is used using fixed-sized all-zero strings in the subkey generation phase to make key-dependent subkeys.
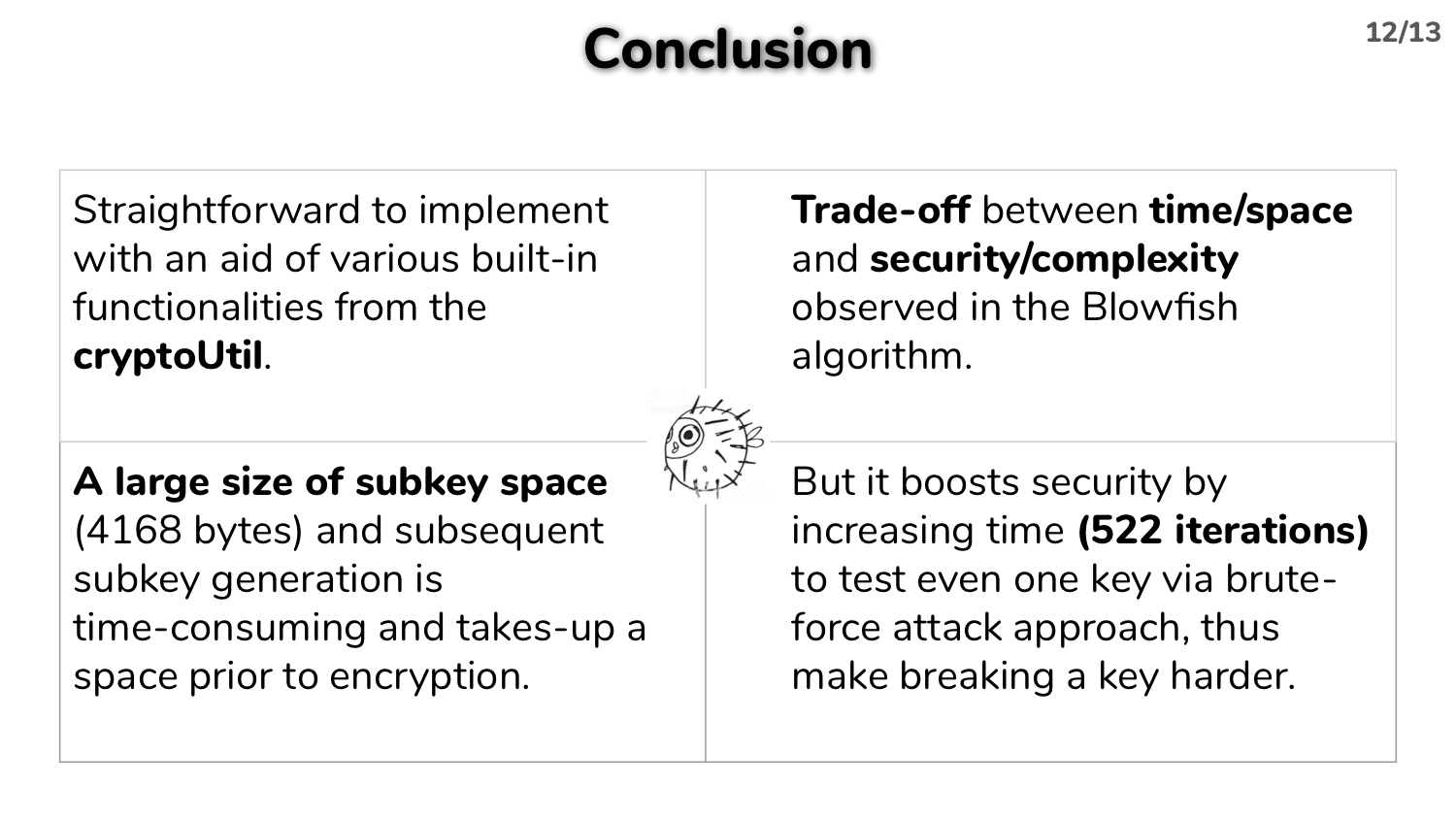
Overall, the Blowfish has many common features with other block ciphers as following, thus I could reuse many methods/classes from the cryptoUtil.
- large S-boxes data structure for lookup;
- combined operations, .e.g. XOR mod 2^32; and
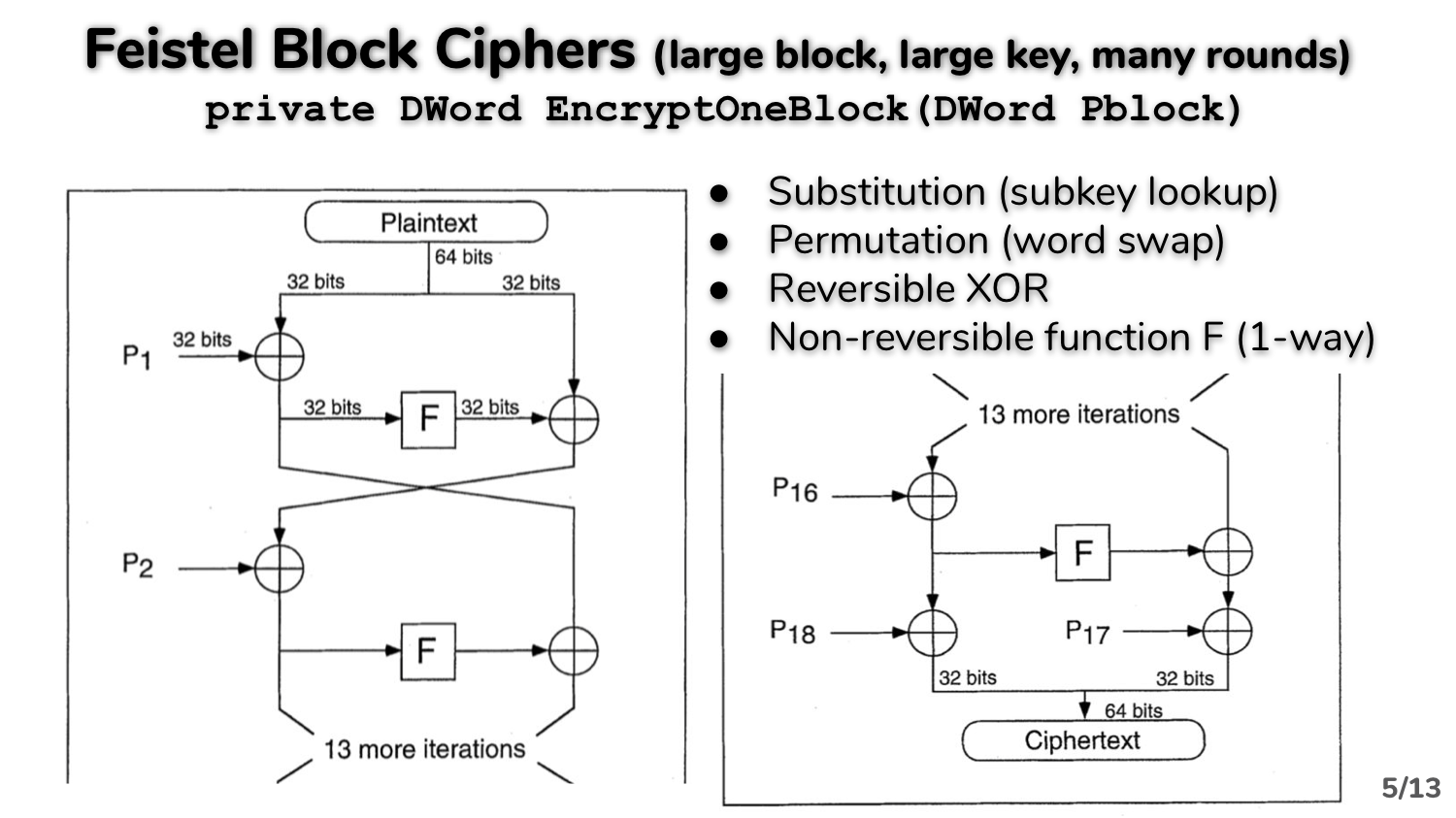
- multiple rounds of Feistel iteration by swapping left and right half of a block